 We Don’t Need to Hack Your Database — We Just Need to Be in the Same Room
We Don’t Need to Hack Your Database — We Just Need to Be in the Same Room
Your CPU leaks secrets through radio waves. Here’s every tool you need to start listening.
Side-channel attacks sound like NSA shit — and they literally were, since 1943. But in 2026, you don’t need a classified budget or a PhD. A $50 board, some free Python scripts, and an afternoon is all it takes to extract an AES encryption key from a live chip. This is the complete dumb-proof starter kit — every repo, every tool, every “plug it in and go” path — organized so you can actually do this, not just read about it.
No prior hardware knowledge. No signal processing background. No bullshit. If you can install Python and plug in a USB cable, you can do this.
🧠 Wait — What Am I Actually Doing Here? (The 60-Second Version)
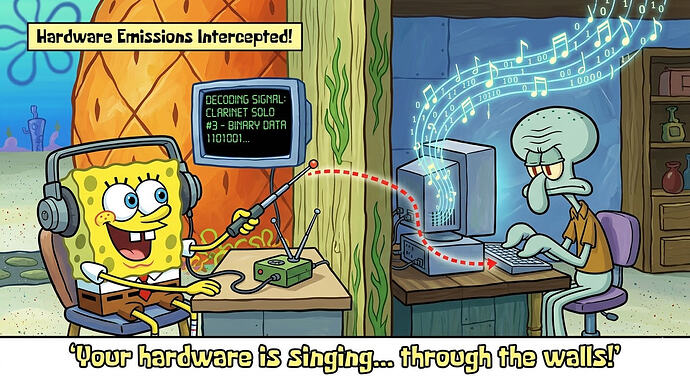
Think of your CPU as a lightbulb that gets slightly brighter or dimmer depending on what it’s thinking about. Every time it processes a “1” instead of a “0,” it draws a tiny bit more power. That power difference creates electromagnetic waves — basically, your processor is a shitty little radio station broadcasting everything it does.
Side-channel attacks listen to that broadcast. Instead of trying to break the math behind encryption (which would take billions of years), you listen to the physical side effects — power consumption, electromagnetic radiation, even sound — and work backwards to figure out what the CPU was processing.
Here’s the wild part: this actually works. Researchers have extracted full encryption keys from laptops using equipment hidden inside a piece of pita bread. Not a joke. The gear cost less than a nice dinner.
| What You’re Doing | How Hard It Is | What You Need |
|---|---|---|
| See your CPU’s power signature | Easy as hell | $50 ChipWhisperer Nano + USB cable |
| Break an AES encryption key | Surprisingly easy | Same $50 board + free Jupyter notebooks |
| Spy on a monitor through walls | Medium (but fun as fuck) | $30 RTL-SDR dongle + free software |
| Train AI to crack encryption | Advanced but doable | Free Python + Google Colab GPU |
💸 The $0 Path — No Hardware, No Excuse
You don’t need to buy a single damn thing to start. Everything below is free, runs in your browser or on any computer, and teaches you the real stuff — not toy simulations.
| Tool | What It Does | Why It’s Dumb-Proof | Link |
|---|---|---|---|
| ChipWhisperer Virtual Labs | Pre-recorded power traces + guided attack notebooks | Literally click-and-run in browser. Zero setup. | learn.chipwhisperer.io |
| PicoCTF Challenges | 3 progressive side-channel CTF problems (Warmup → Part 1 → Part 2) | Software-simulated, no hardware, available year-round, multiple walkthrough writeups exist | picoctf.org |
| Rainbow (Ledger Donjon) | Simulates side-channel leakage from any ARM/x86 binary — generates fake power traces without real hardware | pip install rainbow → feed it a binary → get traces → attack with Lascar |
GitHub |
| ASCAD Dataset | 50,000 real power traces from a masked AES chip — the “MNIST of side-channel analysis” | Download → load in Python → train a neural network → crack the key. Google Colab works perfectly. | GitHub |
| Scared + Binder | Zero-install CPA attack in your browser. eShard hosts Binder notebooks — click, run, break AES. | 15 lines of Python for a complete attack. Has a PicoCTF walkthrough too. | GitHub / PicoCTF writeup |
The fastest path to “holy shit I just broke encryption”: Open the ChipWhisperer virtual labs → run the SCA101 CPA notebook → watch the correlation graph spike on the correct key byte. Takes about 30 minutes. Free. No install.
🔧 The $50 Path — Your First Real Attack
This is where it gets real. You buy one board, plug it in, and extract an actual AES key from a physical chip in your hands.
The board: ChipWhisperer-Nano (~$50)
One USB cable. One board. A built-in target chip (STM32F0) running AES encryption. That’s it. The whole damn lab fits in your pocket.
Step 1 → Install ChipWhisperer:
pip install chipwhisperer
Step 2 → Plug the Nano into USB. Open the SCA101 Jupyter notebook from:
git clone https://github.com/newaetech/chipwhisperer-jupyter.git
Step 3 → Run the notebook cells. The board encrypts data while you record power traces — the notebook handles everything automatically. Capture 50-100 traces. Takes like 2 minutes.
Step 4 → Run the CPA (Correlation Power Analysis) cell. The script tests all 256 possible values for each byte of the key, correlates them against your power measurements, and the correct key pops out as the highest correlation peak.
Total time from unboxing to extracted key: 2-4 hours (including Python setup fuckery). The actual math takes under 60 seconds.
The Nano is limited — 8-bit capture, fixed target, no glitching. For learning? It’s absolutely perfect. Limitations literally don’t matter at this stage.
📡 The $30 Path — Spy on a Monitor Through Walls
Different attack, equally wild. Instead of power analysis, you’re catching electromagnetic emissions from a monitor’s video cable and reconstructing what’s on screen. This is literally what the NSA called TEMPEST.
Shopping list:
| Item | Cost | Where |
|---|---|---|
| RTL-SDR Blog V4 | ~$30 | rtl-sdr.com or Amazon |
| Antenna (included with V4 kit) | $0 | Comes in the box |
| TempestSDR software | $0 | GitHub (RTL-SDR Blog fork) |
Steps:
Step 1 → Install SDR# (free, from airspy.com). Scan 300-700 MHz. Look for signals that visually change when the target monitor’s content changes.
Step 2 → Download TempestSDR from the RTL-SDR Blog fork (NOT the original dormant repo).
Step 3 → Launch JTempestSDR.jar. Enter the target monitor’s resolution and refresh rate. Set the frequency from Step 1.
Step 4 → Click Start. A grayscale reconstruction of the target’s display appears in real-time.
VGA and DVI monitors leak the most. HDMI with shielded cables is harder but not impossible. For dramatically better results, the Deep-TEMPEST fork (GitHub) uses a neural network to clean up the image — drops character error rates from 90% to under 30%.
⚙️ The GitHub Repos That Actually Matter
Not all repos are created equal. Some have 2,000 stars and no documentation. Some have 50 stars and will teach you everything. Here’s what’s actually worth your time.
The Big Five — Start Here:
| Repo | Stars | What It Does | Beginner Score | Link |
|---|---|---|---|---|
| ChipWhisperer | 1,400+ | Complete hardware + software toolkit for power analysis and glitching | GitHub | |
| chipwhisperer-jupyter | — | The actual tutorials. Structured courses (SCA101, SCA201, Fault101) as Jupyter notebooks. | GitHub | |
| Lascar (Ledger Donjon) | 404 | Full attack pipeline: SNR, CPA, DPA, template attacks, deep learning. Built by Ledger’s security team. | GitHub | |
| SCAAML (Google) | 191 | ML-powered side-channel analysis. Their GPAM model cracked AES from just 4 power traces. | GitHub | |
| Scared (eShard) | ~88 | Fastest CPA implementation. A full attack in ~15 lines of Python. Binder notebooks for zero-install. | GitHub |
Specialized Tools:
| Repo | What It Does | Use Case | Link |
|---|---|---|---|
| TempestSDR (RTL-SDR fork) | Reconstructs monitor display from EM emissions in real-time | Screen eavesdropping with $30 SDR | GitHub |
| Deep-TEMPEST | Neural network enhancement for TempestSDR — way clearer image recovery | Makes TempestSDR actually readable | GitHub |
| gr-tempest | GNU Radio blocks for TEMPEST attacks with pre-built flowgraphs | Advanced SDR users | GitHub |
| Rainbow (Ledger) | Side-channel simulator — generates traces from binaries without hardware | Practice attacks with zero hardware | GitHub |
| SCALib | Python/Rust hybrid — 117× faster than Lascar for SNR computation | When Lascar is too slow | GitHub |
| EMMA | EM capture via SDR + neural network attacks (FOSDEM 2019 demo) | Historical — cool but dormant since 2020 | GitHub |
| PicoEMP | Raspberry Pi Pico-based electromagnetic fault injector | Glitch chips with EM pulses (~$50 DIY) | GitHub |
| awesome-side-channel-attack | Curated master list of everything — tools, papers, datasets, conferences | Your bookmark for “what else is out there” | GitHub |
💰 Hardware Buying Guide — Every Budget Level
| Budget | What to Buy | What You Can Do | Link |
|---|---|---|---|
| $0 | Nothing — virtual labs + datasets | Learn CPA theory, solve CTFs, train ML models on real traces | learn.chipwhisperer.io |
| $30 | RTL-SDR Blog V4 | Spy on monitor displays, observe CPU EM emissions, listen to processors work | Amazon or rtl-sdr.com |
| $50 | ChipWhisperer-Nano | Break AES on a real chip in your hands. The gateway drug. | store.newae.com |
| $80 | Nano + DIY coax loop probe ($5) + RTL-SDR ($30) | Power analysis AND electromagnetic observation | — |
| $325 | ChipWhisperer-Lite | 10-bit capture + voltage/clock glitching — attack more targets | store.newae.com |
| $549 | ChipWhisperer-Husky Starter Kit | 12-bit 200MS/s + streaming mode — attack RSA, ECC, and asymmetric crypto | Crowd Supply |
| $330 | Tekbox TBPS01 probe set + amplifier | Professional EM near-field probes for precise chip-level measurement | tekbox.com / Amazon |
| $1,050 | Husky Kit + Tekbox probes + PicoEMP + RTL-SDR | The complete lab: power analysis, EM side-channel, fault injection, broadband capture | — |
Honest take: Start at $50 with the Nano. If you’re still doing this a month later, jump to the Husky. Everything else is “when you know what you’re looking for.”
📚 Learning Path — Zero to Key Extraction
Phase 1: Understand WTF is happening (free, 1-2 days)
| Resource | Format | Time | Link |
|---|---|---|---|
| Cloudflare — Hertzbleed Explained | Blog post — best beginner explainer of how power = vulnerability | 20 min read | cloudflare.com |
| ChipWhisperer Power Analysis 101 | Online course with virtual labs — no hardware needed | 2-4 hours | learn.chipwhisperer.io |
| FOSDEM 2019 — EM Attacks with RTL-SDR | Video talk by Pieter Robyns — attacking AES on an Arduino with a $25 SDR | 30 min | FOSDEM archive |
Phase 2: Break something (free or $50, 1 weekend)
| Resource | Format | Time | Link |
|---|---|---|---|
| PicoCTF side-channel challenges | Browser-based CTF — 3 progressive power analysis problems | 2-3 hours | picoctf.org |
| SCA101 Jupyter notebooks | Hands-on with Nano or virtual traces — from first trace to full AES key | 4-6 hours | GitHub |
| eShard PicoCTF writeup | Step-by-step walkthrough using the scared library |
1-2 hours | eshard.com |
Phase 3: Go deeper (weeks to months)
| Resource | Format | Cost | Link |
|---|---|---|---|
| TU Graz Side-Channel Security (edX) | 6-season video course — from software side-channels to Meltdown/Spectre. Season 4 = power/EM analysis. | Free audit / $129 cert | edX |
| The Hardware Hacking Handbook | Book by Colin O’Flynn (ChipWhisperer creator). ~1/3 is power analysis with lab exercises. | ~$40-50 | No Starch Press / hardwarehacking.io |
| Coursera Hardware Security (UMD) | University course — Week 4 covers side-channel attacks | Free audit | Coursera |
| Hacker’s Guide to DL Side-Channel Attacks | Blog series + code walkthrough for ML-powered attacks | Free | elie.net |
| CHES Challenge | Annual competition — 2025 was “GE Wars” (DL SCA on Raspberry Pi traces) | Free | ches.iacr.org |
Phase 4: ML + advanced shit
| Resource | What | Link |
|---|---|---|
| ASCAD dataset + Google Colab | Train a CNN to break masked AES — runs free on Colab with GPU | GitHub |
| Google SCAAML notebooks | Pre-trained models that crack AES from 4 traces | GitHub |
| 2025 IACR DL-SCA Tutorial | Most up-to-date walkthrough — includes a Colab notebook | |
| Scadl (Ledger) | Deep learning SCA tool — profiling + non-profiling attacks | GitHub |
🎧 Bonus: Hear Your CPU Think
This one’s just for fun. You can literally listen to your processor working with a $30 SDR.
How: Tune your RTL-SDR to harmonics of your target’s clock frequency. For a 16 MHz Arduino, try 32 MHz (2× harmonic) or 48 MHz (3×).
Quick spectrum sweep:
rtl_power -f 1M:500M:100k -g 40 -i 1 scan.csv
In SDR# with AM demodulation, CPU-heavy operations produce audible buzzing that stops when computation ends. Run a tight loop on the Arduino → hear the buzz. Stop the loop → silence.
What you can visually see in a power trace:
- RSA: Each private key bit is visible — a “0” creates a short spike (square only), a “1” creates a taller spike (square + multiply). The entire key is right there in the graph.
- AES: All 10 rounds show up as repeating power clusters. S-box lookups create spikes whose height correlates with the actual data.
This isn’t theoretical. This is “open the notebook, look at the graph, read the key.”
![]() Quick Hits
Quick Hits
| Want | Do |
|---|---|
| → ChipWhisperer virtual labs — free, 30 minutes, zero install | |
| → ChipWhisperer-Nano — break AES on a real chip in your hands | |
| → RTL-SDR V4 + TempestSDR | |
| → ASCAD dataset + Google Colab (free GPU) | |
| → awesome-side-channel-attack | |
| → Rainbow + Lascar — simulate + attack entirely in software |
Your encryption is only as strong as the physics around it. Now you know how to listen.
 !
!